Sep 14, 2022
You are almost ready to move your business applications, data, and infrastructure to the Cloud but you still need to be a little bit more confident.
These 4 pillars represent the main value proposition for what differentiates Azure from the competition.
Those are the reasons why customers choose Microsoft, because of the unique value that we provide in a productive, hybrid, intelligent, and trusted cloud.
Jul 8, 2022
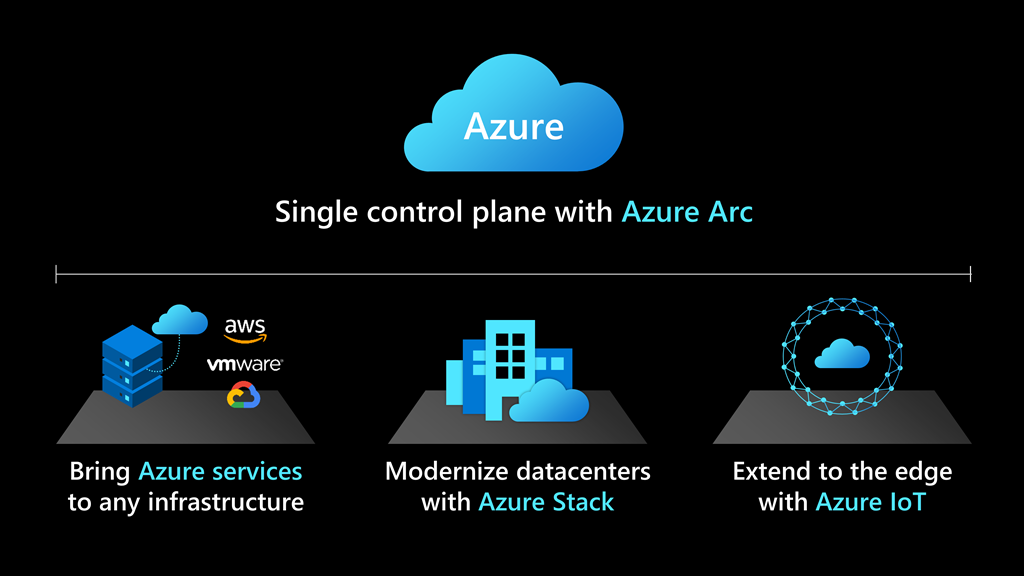
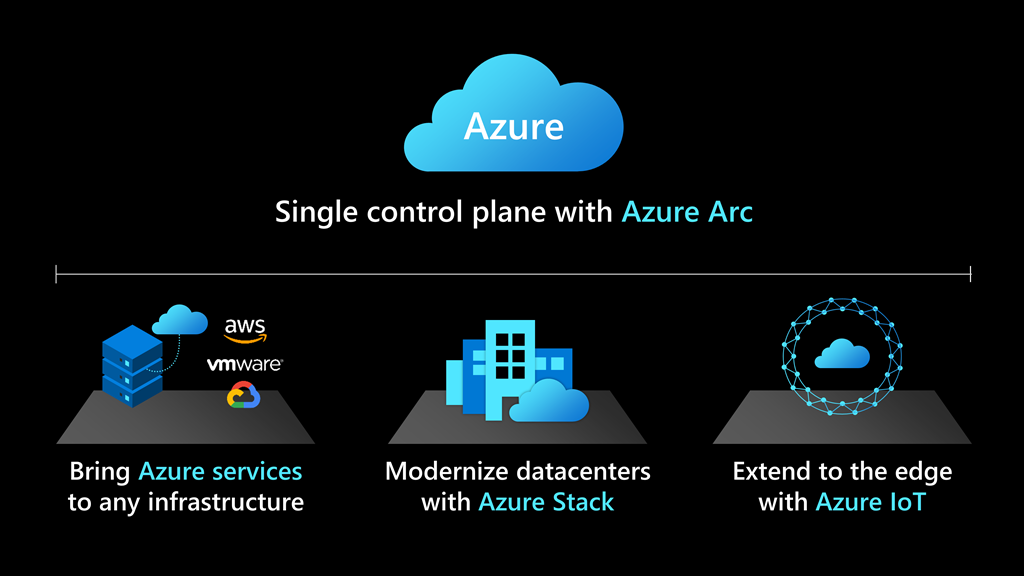
Customers can deploy cloud services on-premises and in multi-cloud environments—effectively modernizing in place by running Azure SQL on any infrastructure.
Cloud solutions that simplify the most complex hybrid data scenarios
Deploying cloud-based solutions to on-premises and multi-cloud environments helps deliver consistent, portable, and unified management across a company’s entire data estate. Customers are seeing improved productivity and operating efficiency by using hybrid technology to manage their data and app development at scale.
For example, SKF provides reliable rotation to industries all over the world, offering products and services around the rotating shaft including bearings, seals, lubrication management, artificial intelligence, and wireless condition monitoring. SKF has been on a journey to digitally transform the company’s backbone through harnessing the power of technology, interconnecting processes, streamlining operations, and delivering industry-leading digital products and services for customers. SKF uses Azure Arc, along with Azure Stack HCI and Azure SQL Edge, to scale solutions and standardize processes across their 91 manufacturing sites, resulting in 40 percent savings on hardware costs and 30 percent savings in OT-related machine downtime.
“SKF’s focus is on digitalizing all segments of the value chain and interconnecting them to unlock the full potential of digital ways of working for our business and customers. Azure Arc-enabled SQL Managed Instance is providing us worry-free and always up-to-date SQL operations. These types of services provide us a tremendous jumpstart into digitalization.”—Sven Vollbehr, Head of Digital Manufacturing, SKF
The “anywhere” solution for hybrid cloud applications
Beginning July 30, 2021, the general-purpose tier of Azure Arc-enabled SQL Managed Instance will be generally available, providing database-as-a-service (DBaaS) functionality on any infrastructure. Businesses will be able to deploy Azure SQL databases on any infrastructure and on any Kubernetes to:
- Stay current with automated updates and deploy evergreen features and security updates to on-prem databases with no end-of-support.
- Automate routine database administrator (DBA) tasks at scale with built-in management capabilities including high availability, backup, and restore.
- Optimize data workload performance by bringing cloud elasticity on-premises for existing infrastructure, using only the resources needed to dynamically scale up, down, without application downtime.
- Access Azure industry-leading security and governance capabilities for your on-premises data workloads using to protect your data.
New product features and capabilities will be rolled out on a continuous basis, and customers will be able to opt-in to preview additional Azure Arc-enabled services, such as PostgreSQL, and easily integrate as they become generally available. Additionally, customers will have the opportunity to test out future road map preview features and provide early feedback.
Develop breakthrough applications with our network of trusted partners
In support of Azure Arc-enabled data services’ general availability, Microsoft is announcing an expanded network of trusted partners and validated solutions to help customers get started.
Microsoft works closely with technology providers to validate popular platforms to work with Azure Arc, and our many service providers are here to provide customers with the latest innovations for hybrid data solutions on-premises or in multi-cloud environments.
Whether you are just getting started with migration and modernization efforts or in the middle of a multi-year digital transformation, our consulting services partners can help you choose the validated infrastructures and applications that are specifically configured and tested to work with Azure Arc.
Get started with Azure Arc-enabled data services
Get started with Azure Arc-enabled data services available in preview today. Starting July 30, 2021, Azure Arc-enabled SQL Managed Instance (general-purpose tier) will be generally available for customers to optimize their data workloads from cloud to edge.
Contact us to learn more on [email protected]
May 19, 2022
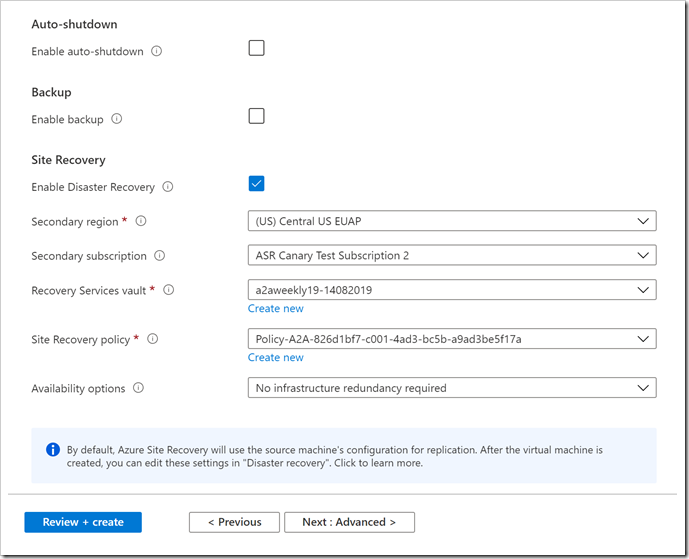
Microsoft has lately announced a new capability in Azure Site Recovery to further improve the Business Continuity and Disaster Recovery posture of Azure VMs – in-line enablement of ASR at the time of VM creation.
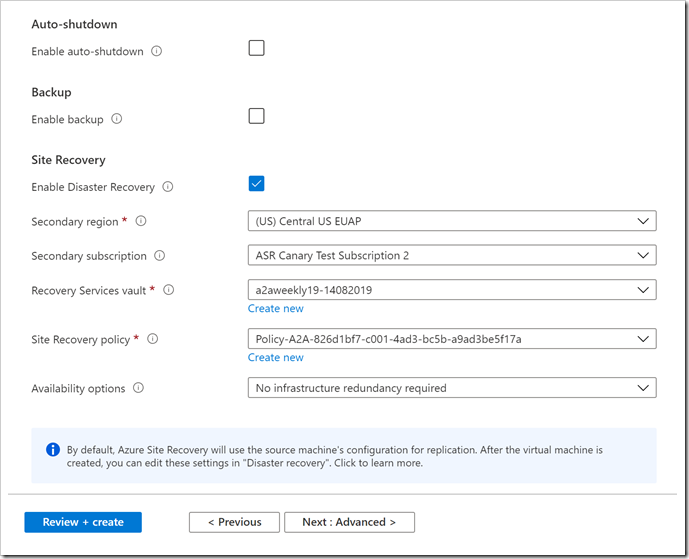
This capability helps all Azure infrastructure customers avoid the hassle of separately configuring DR across regions (or zones) after the creation of VMs.
Microsoft recognizes that as the customers move and more business-critical applications to Azure, their resilience is of prime importance.
ASR is a key pillar of Microsoft’s resiliency offering, which allows customers to protect their Azure VMs against regional outages.
Previously, there was no seamless way to enable ASR during the creation of a VM. End customers had to follow through and execute a different workflow to protect the VM from regional (or zonal) outages after the VM was up and running.
With Microsoft latest release, now all end customers will be able to enable ASR while creating a VM. ASR will be one of the VM Management options alongside the ones currently available for configuration – Monitoring, Identity, and Backup, among others.
To get started, a customer can simply head over to the Azure portal. Go to ‘Virtual machines’ and click on ‘+ Add’. Go to the Management tab and select ‘Enable Disaster Recovery’ under ‘Site Recovery’. Make the relevant selections and proceed to create Azure VM. Once the VM is created, replication will be automatically enabled within a few minutes.
It shall be noted that so far, this offering is currently limited to Windows VMs and CentOS, Oracle Linux, and Red Hat Linux VMs. Microsoft also do not support zone to zone (in region) disaster recovery through the Create VM workflow currently.
Aug 5, 2021
Azure Firewall Premium provides next-generation firewall(NGFW) capabilities that are required for highly sensitive and regulated environments.
With the new Azure Firewall Premium, the following new capabilities are now available:
- TLS Inspection: Azure Firewall Premium terminates outbound and east-west TLS connections. Inbound TLS inspection is supported in conjunction with Azure Application Gateway allowing end-to-end encryption. Azure Firewall performs the required value-added security functions and re-encrypts the traffic which is sent to the original destination.
- IDPs: Azure Firewall Premium provides signature-based intrusion detection and prevention system (IDPs) to allow rapid detection of attacks by looking for specific patterns, such as byte sequences in network traffic, or known malicious instruction sequences used by malware.
- Web Categories: Allows administrators to allow or deny user access to the Internet-based on categories (e.g. social networking, search engines, gambling), reducing the time spent on managing individual FQDNs and URLs. This capability is also available for Azure Firewall Standard based on FQDNs only.
- URL Filtering: Allow users to access specific URLs for both plain text and encrypted traffic, typically being used in conjunction with Web Categories.
Azure Firewall Premium is utilizing Firewall Policy, a global resource that can be used to centrally manage your firewalls using Azure Firewall Manager. Starting this release, all new features will be configurable via Firewall Policy only. This includes TLS Inspection, IDPS, URL Filtering, Web categories, and more. Firewall Rules (Classic) continue to be supported and can be used for configuring existing features of Standard Firewall. Firewall Policy can be managed independently or using Azure Firewall Manager. A firewall policy associated with a single firewall has no charge.
For more information, see the Azure Firewall Premium documentation
Jun 10, 2021
As a cloud-native SIEM, Azure Sentinel offers significant cost benefits. They have seen Azure Sentinel and the promise of cloud-native SIEM result in cost savings, both direct and indirect, for many of their customers. The 2020 commissioned Forrester Consulting Total Economic Impact™ of Microsoft Azure Sentinel study, for example, found that Azure Sentinel delivered a 48% reduction in costs compared to legacy SIEMs, saving on expenses like licensing, storage, and infrastructure costs.
Microsoft are pleased to announce changes to the pricing of Azure Sentinel and Azure Monitor Log Analytics that will offer you additional cost savings. These changes take effect on June 2.
The changes include:
New capacity reservation naming
Capacity reservations are now called commitment tiers. You will see this change reflected in your user interface, in documentation, as well as on Azure Sentinel and Azure Monitor pricing pages and in the pricing calculator.
New, higher commitment tiers
They are introducing new commitment tiers for both Azure Sentinel and Azure Monitor Log Analytics for higher data ingestion: 1 TB/Day, 2 TB/Day, and 5 TB/Day.
Changes to how we bill for data ingestion over your commitment tiers
They are also changing the way we bill for overage. Data ingested beyond your selected commitment tier will now be billed using the effective commitment tier rate, instead of the Pay-as-you-go rate, resulting in a lower bill.
For example, for Azure Sentinel in the East US region, if you are on a 500 GB/day commitment tier, you will now be billed for overage at $0.80/GB (i.e. the effective rate for that tier) instead of the $2/GB pay-as-you-go rate.
Simplification of commitment tiers
They are simplifying commitment tiers to make them easier to manage. You can now select from eight distinct commitment tiers, per your needs, and no longer need to manage tiers due to minor changes in data ingestion patterns.
As part of this change, any workspaces with commitment tiers greater than 500 GB/day will be reset to the lowest available commitment tier – 500 GB/day, 1 TB/day, 2 TB/day, or 5 TB/day. This change should lower your costs due to the lowered cost of overage.
For example, if you were previously on a 600 GB/day commitment tier, your commitment tier would now be to 500 GB/day. Due to the change in overage billing, on days when you ingest more than 600GB, you would get billed at the 500GB effective tier rate, and on days you ingest less than 600GB, you save money because you are at a lower commitment tier – saving you costs overall.
Learn More
We’re excited to help you save costs with these changes, and look forward to continuing to innovate with Azure Sentinel and Azure Monitor Log Analytics.
Mar 11, 2021
Azure UAE Regions are now stronger than ever with the availability of the new Azure Services led by Azure Security!

The new services are:
Azure Sentinel has the capability to see and stop threats before they cause harm, with a SIEM and SOAR reinvented for a modern world, providing a birds-eye view across the enterprise.
Artificial intelligence (AI) makes threat detection and response smarter and faster. The platform allows for elastic scaling and eliminates the need for costly set up and maintenance. For these reasons, customers such as ASOS are leveraging Azure Sentinel to analyze data coming from separate systems and solutions.
Azure Bastion is a fully managed PaaS service that provides secure and seamless RDP and SSH access to virtual machines directly through the Azure Portal. Azure Bastion is provisioned directly in a customer’s Virtual Network (VNet) and supports all VMs using SSL without any exposure through public IP addresses.
Cognitive Services: Immersive Reader and Anomaly Detector
- Immersive Reader is an Azure Cognitive Service that allows for embedding text reading and comprehension capabilities into applications. Users of any age and reading ability are supported with features like reading aloud, translating languages, and focusing attention through highlighting and other design elements. Azure is the only major cloud provider offering this type of reading technology. No machine learning expertise is required.
- Anomaly detection capabilities can be easily embedded into apps so users can quickly identify problems. Through an API, Anomaly Detector ingests time-series data of all types and selects the best-fitting detection model for particular data to ensure high accuracy. The service can be customized to detect any level of anomaly and deployed where need it is needed most inside containers – from the cloud to the intelligent edge. Azure is the only major cloud provider that offers anomaly detection as an AI service.
This application can connect with business-critical apps and services, automating workflows without writing a single line of code. Its advantages include leveraging a write-once, run anywhere ability, a consistent integration with developer tools and services, creating business processes and workflows visually and integrating with SaaS and enterprise applications.
- Container Instances & App Configuration
Container Instances and App Configuration provide simplicity, scalability and security while modernizing applications.
Security and Protection, Artificial Intelligence, Cognitive Services, Application Integration and Modernization are leading this round of the new services announcement.