Sep 8, 2022
Microsoft officially announced the public preview to a simpler and more reliable way to protect your VMware virtual machines.
To tackle the changing needs of the customers, they have performed a major overhaul of the hybrid disaster recovery and added necessary enhancements along with highly requested simplifications. They have implemented a new architecture with which, the configuration server has now been revamped as the ASR replication appliance.
Automatic upgrades for ASR replication appliance and Mobility agent
A big deal-breaker with the current architecture was manually updating various configuration server components and mobility services. – as soon as an update arrives, both the appliance and mobility service will be updated automatically and that too out of business hours.
Additionally, for automatic upgrades, machine credentials will not be required anymore. Currently, it is necessary to have the latest credentials for both Linux and Windows machines for a successful update. But with this preview, the credentials will be required only initially and will not be required once the installation is complete. After the installation of the mobility service, credentials can be removed for all the machines.
Easier scale management
The appliance is now a single unit of management and all its components have been converted into micro-services which are hosted on Azure. This will not only make the troubleshooting much easier, but scale management also becomes much smoother. To scale out an appliance, you will just need to set up another appliance and voila, it is done! No need to set up another Process server anymore.
High availability for appliance
Appliance resiliency has also been a highly asked about topic and we have that covered too. Customers are usually afraid of an appliance burndown. There are also scenarios where one may need to load balance an appliance and move a protected machine to another appliance, without disabling replication.
With the preview, you don’t need to take regular backups of your appliance anymore – just spin up another appliance and switch all your machines to the new appliance. All the configuration details particular to a protected machine will be switched to the new appliance without needing to go through the complete replication again.
Apart from the above-mentioned improvements, they have also removed –
- passphrase dependency – implemented a new certificate-based authentication,
- static IP address dependency – will rather use FQDNs to maintain connectivity,
- third party product dependency – MySQL installation on the appliance will not be required anymore.
Learn more about the preview architecture and check out the release notes for a detailed list of improvements.
Sep 8, 2021
Microsoft is announcing changes to the commercial pricing for Microsoft 365—the first substantive pricing update since they’ve launched Office 365 a decade ago.
This updated pricing reflects the increased value Microsoft has delivered to its customers over the past 10 years.
Take a look at some of the innovations they’ve delivered over the past decade in three key areas—communications and collaboration, security and compliance, and AI and automation—as well as the addition of audio conferencing capabilities that they’re announcing today.
A decade of continuous innovation
Since introducing Microsoft 365 they have added 24 apps1 to the suites—Microsoft Teams, Power Apps, Power BI, Power Automate, Stream, Planner, Visio, OneDrive, Yammer, and Whiteboard—and have released over 1,400 new features and capabilities in three key areas.
→ Communication and collaboration.
In 2020 Microsoft released over 300 new capabilities including Together mode, background effects, large gallery view, raise a hand, live reactions, breakout rooms, live captions with speaker attribution, and Fluid components, just to name a few.
- They introduced a new category of collaborative applications in Teams, empowering people and organizations for hybrid work through deep integrations with Power Platform, Whiteboard, Lists, Planner, Shifts, Forms, and SharePoint. Companies like Adobe, Atlassian, Salesforce, SAP, ServiceNow, and Workday have built apps that deeply integrate with Teams, bringing business processes and functions directly into the flow of work.
- They continue to innovate on both real-time and asynchronous collaboration.
- They introduced real-time collaboration in Word, Excel, and PowerPoint desktop apps while a growing set of capabilities like @mentions, assign tasks, modern comments, and auto-save have streamlined the collaboration experience.
- They’ve added and expanded OneDrive cloud storage and the Exchange Online mailboxes.
→ Security and compliance.
- The cybersecurity landscape is more complex than ever. With the accelerating volume, sophistication, and scale of cyberattacks, security and compliance are a priority for every organization. Since they first introduced Microsoft 365, they have added new attack surface reduction capabilities to help organizations defend against ransomware and other threats.
- They have added capabilities like data loss prevention (DLP) for email and documents, sensitivity labels, and message encryption to help keep important data within the organization.
- They have added powerful compliance capabilities that help organizations reduce risk and respond to increasing regulatory requirements such as Content Search, eDiscovery, and core Litigation Hold. Built-in mobile device management (MDM) and other management tools like Microsoft Endpoint Manager help admins support remote and hybrid workforces.
→ AI and automation.
- Over the past decade, they have infused AI capabilities across our productivity and collaboration applications to help everyone achieve more.
- Across Microsoft 365, they have introduced AI-powered innovations to help users be better writers, designers, and presenters.
- Cloud-powered AI now automatically creates maps, charts, and tables in Excel, and sorts email and removes clutter in Outlook. And AI-powered real-time translation, captions, and transcription make collaboration and communication more accessible and engaging for everyone.
Extending audio conferencing capabilities
- Microsoft is announcing that they will add unlimited dial-in capabilities for Microsoft Teams meetings across our enterprise, business, frontline, and government suites over the next few months. Even as cloud connectivity increases, they know that people join Teams meetings while they are on the go or struggling with a bad internet connection.
- Currently included with Microsoft 365 E5 and Office 365 E5, they have come to see dial-in as an important part of the complete Teams experience.
- Available with subscriptions in over 70 countries and with interactive support in 44 languages and dialects, unlimited dial-in provides peace of mind that users will be able to join their Microsoft Teams meeting from virtually any device regardless of location.
New pricing
- The pricing changes Microsoft is announcing today will go into effect in six months.
- On March 1, 2022, they will update our list pricing for the following commercial products: Microsoft 365 Business Basic (from $5 to $6 per user), Microsoft 365 Business Premium (from $20 to $22), Office 365 E1 (from $8 to $10), Office 365 E3 (from $20 to $23), Office 365 E5 (from $35 to $38), and Microsoft 365 E3 (from $32 to $36).
- These increases will apply globally with local market adjustments for certain regions.
- There are no changes to pricing for education and consumer products at this time.
- As leaders around the world look to empower their people for a more flexible, hybrid world of work, it’s clear that every organization will need a new operating model across people, places, and processes. Microsoft is committed to building on the value they’ve delivered over the past decade to continuously provide innovation that helps our customers succeed and thrive today and well into the future.
Click to learn more
Contact us to learn more [email protected]
Sep 7, 2021
Non-genuine software is a cybersecurity risk
Software piracy is a widespread global problem. Cybercriminals are exploiting non-genuine
software to spread malware, and users are exposing themselves to multiple security risks.
The reach and risk of counterfeit goods

Easy Mistakes
39% of inadvertent purchases of counterfeit goods were bought through legitimate online third-party marketplaces.

Pervasive Supply
Half a trillion US dollars’ worth of imports across the world are counterfeit products.

Increased Malware
20% more malware was found on machines when users doubled their time on piracy sites.
The confidence to move forward
Microsoft genuine software provides the security, updates, and support you need. Get the best experience, build trust, and avoid risk—buy Microsoft genuine software.
Risks of non-genuine software
Think twice before your next purchase.
Non-genuine software may come with viruses and would lack the security measures needed to detect them.
You may be opening your home or business to serious threats from hackers and malware without knowing it.
Malware
Malware can contain ransomware, which may block access to data or user accounts unless a ransom is paid.
Reputation and material damage
Hackers can destroy your business data and other valuable information. These security breaches may harm your image and erode customer trust.
Your personal and financial data may be compromised, which may result in financial damage. It could even be used for criminal activities.
- Stolen credit card or bank details
Hackers can clone your credit card and access your bank accounts, resulting in financial loss for you or your business.
A data breach can bring your entire business operation to a halt and harm your website, CRM, and accounting systems.
You could lose important personal files and business data, like customer and accounting information.
How do I know I’m using genuine software?
Make sure it’s licensed.
 Before purchasing a new PC, make sure genuine Windows is pre-installed on the device.
Before purchasing a new PC, make sure genuine Windows is pre-installed on the device.
 All Windows PCs must have a license, which allows you to upgrade your version through volume licensing.
All Windows PCs must have a license, which allows you to upgrade your version through volume licensing.
 Volume licensing agreements only cover Windows software upgrades. Only PCs are bundled with a full base license (OEM/GGWA/FPP/ESD).
Volume licensing agreements only cover Windows software upgrades. Only PCs are bundled with a full base license (OEM/GGWA/FPP/ESD).
 Consumer versions of Windows are NOT eligible for volume licensing upgrades to Windows Professional.
Consumer versions of Windows are NOT eligible for volume licensing upgrades to Windows Professional.
 Get Genuine Windows Agreement (GGWA) is the legalization solution for corporate users who want to legitimize Windows Professional licenses on existing devices. For all new devices, Original Equipment Manufacturer (OEM) base licenses are required.
Get Genuine Windows Agreement (GGWA) is the legalization solution for corporate users who want to legitimize Windows Professional licenses on existing devices. For all new devices, Original Equipment Manufacturer (OEM) base licenses are required.
How do I avoid non-genuine software?
Follow this software purchasing guide.
 Be the first to open it
Be the first to open it
A physical product’s package must be sealed to ensure first-time use. Product keys are designed to work on a single or limited number of devices.
Stay up to dateRun software updates regularly to help stay protected against potential security issues.
A reputable reseller or the Microsoft Store are your go-to options.
 Question “too-good-to-be-true” prices
Question “too-good-to-be-true” prices
They usually are—and may lead to additional costs from data loss or identity theft.
- Check the product key source
For digital downloads, make sure the product key comes from a trusted source and not an instant messaging platform or unverifiable email.
Make sure physical packaging includes an authentic Microsoft logo and brand identity. Be wary of standalone stickers or product key cards, which don’t grant the right to use Microsoft software.
A physical product’s package must be sealed to ensure first-time use. Product keys are designed to work on a single or limited number of devices.
Run software updates regularly to help stay protected against potential security issues.
A reputable reseller or the Microsoft Store is your go-to option.
 Use only licensed software
Use only licensed software
Software must be properly licensed, whether it’s Windows or Office.
Buy Microsoft genuine software
 Digital Downloads
Digital Downloads
Avoid the many risks of digital downloads with these tips for safer shopping.
Learn More
Aug 5, 2021
Azure Firewall Premium provides next-generation firewall(NGFW) capabilities that are required for highly sensitive and regulated environments.
With the new Azure Firewall Premium, the following new capabilities are now available:
- TLS Inspection: Azure Firewall Premium terminates outbound and east-west TLS connections. Inbound TLS inspection is supported in conjunction with Azure Application Gateway allowing end-to-end encryption. Azure Firewall performs the required value-added security functions and re-encrypts the traffic which is sent to the original destination.
- IDPs: Azure Firewall Premium provides signature-based intrusion detection and prevention system (IDPs) to allow rapid detection of attacks by looking for specific patterns, such as byte sequences in network traffic, or known malicious instruction sequences used by malware.
- Web Categories: Allows administrators to allow or deny user access to the Internet-based on categories (e.g. social networking, search engines, gambling), reducing the time spent on managing individual FQDNs and URLs. This capability is also available for Azure Firewall Standard based on FQDNs only.
- URL Filtering: Allow users to access specific URLs for both plain text and encrypted traffic, typically being used in conjunction with Web Categories.
Azure Firewall Premium is utilizing Firewall Policy, a global resource that can be used to centrally manage your firewalls using Azure Firewall Manager. Starting this release, all new features will be configurable via Firewall Policy only. This includes TLS Inspection, IDPS, URL Filtering, Web categories, and more. Firewall Rules (Classic) continue to be supported and can be used for configuring existing features of Standard Firewall. Firewall Policy can be managed independently or using Azure Firewall Manager. A firewall policy associated with a single firewall has no charge.
For more information, see the Azure Firewall Premium documentation
Mar 11, 2021
Azure UAE Regions are now stronger than ever with the availability of the new Azure Services led by Azure Security!

The new services are:
Azure Sentinel has the capability to see and stop threats before they cause harm, with a SIEM and SOAR reinvented for a modern world, providing a birds-eye view across the enterprise.
Artificial intelligence (AI) makes threat detection and response smarter and faster. The platform allows for elastic scaling and eliminates the need for costly set up and maintenance. For these reasons, customers such as ASOS are leveraging Azure Sentinel to analyze data coming from separate systems and solutions.
Azure Bastion is a fully managed PaaS service that provides secure and seamless RDP and SSH access to virtual machines directly through the Azure Portal. Azure Bastion is provisioned directly in a customer’s Virtual Network (VNet) and supports all VMs using SSL without any exposure through public IP addresses.
Cognitive Services: Immersive Reader and Anomaly Detector
- Immersive Reader is an Azure Cognitive Service that allows for embedding text reading and comprehension capabilities into applications. Users of any age and reading ability are supported with features like reading aloud, translating languages, and focusing attention through highlighting and other design elements. Azure is the only major cloud provider offering this type of reading technology. No machine learning expertise is required.
- Anomaly detection capabilities can be easily embedded into apps so users can quickly identify problems. Through an API, Anomaly Detector ingests time-series data of all types and selects the best-fitting detection model for particular data to ensure high accuracy. The service can be customized to detect any level of anomaly and deployed where need it is needed most inside containers – from the cloud to the intelligent edge. Azure is the only major cloud provider that offers anomaly detection as an AI service.
This application can connect with business-critical apps and services, automating workflows without writing a single line of code. Its advantages include leveraging a write-once, run anywhere ability, a consistent integration with developer tools and services, creating business processes and workflows visually and integrating with SaaS and enterprise applications.
- Container Instances & App Configuration
Container Instances and App Configuration provide simplicity, scalability and security while modernizing applications.
Security and Protection, Artificial Intelligence, Cognitive Services, Application Integration and Modernization are leading this round of the new services announcement.
Dec 11, 2020
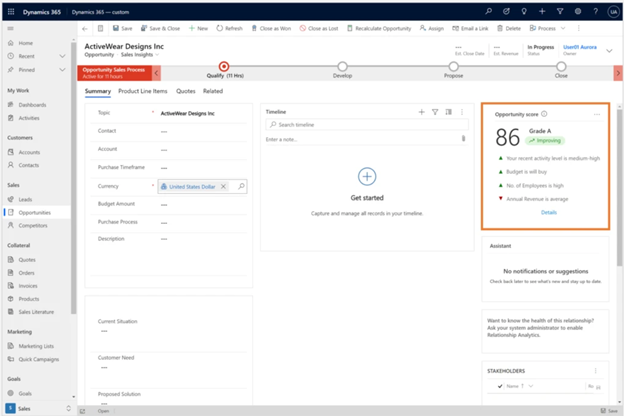
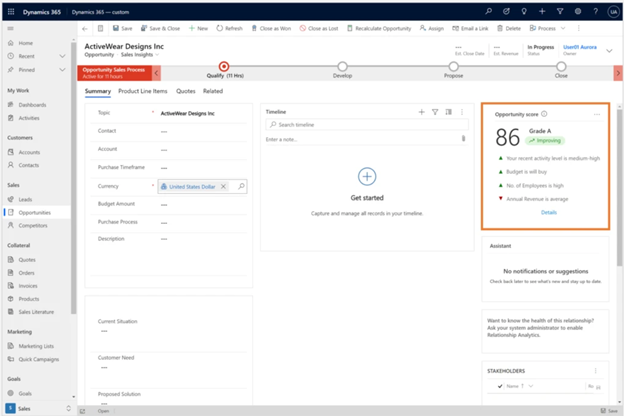
Microsoft has developed new capabilities in Dynamics 365 to discover email messages, meetings, and
phone call activities related to an opportunity, and then to factor these signals into the score.
Capturing activities to determine opportunity health
A healthy opportunity will usually have activities happening in it like email messages, meetings, and phone
calls.
Many of our predictive opportunity scoring customers were gathering these signals manually to determine
opportunity health.
Microsoft has replaced the need for customers to manually track activities by using AI to gather activities,
approving prediction accuracy, and compensating for cases where sellers do not diligently update the
opportunity fields.
This can help the seller make more educated choices about what the best next action might be.
For example, a high level of activity may indicate that the opportunity is heating up and is worth attention.
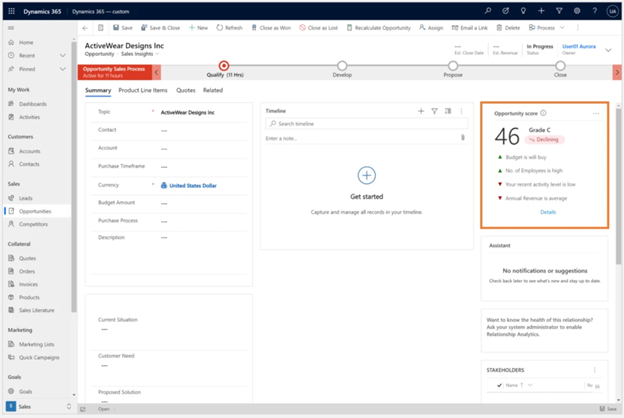
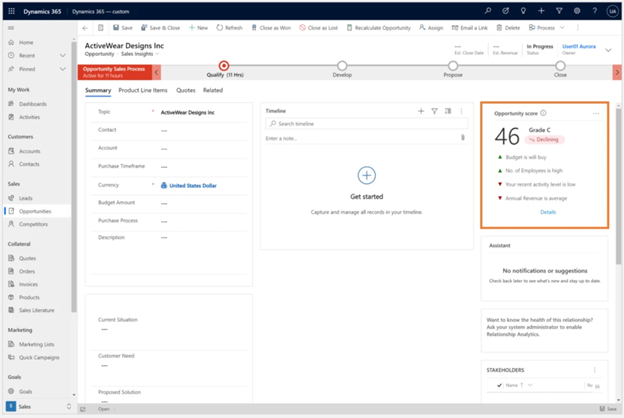
Likewise, an opportunity with where the activity level is low may need immediate attention.
Here’s an example showing the opportunity score improving
Here's an example showing the opportunity score declining:
Connecting opportunities with activities
In addition to activities that are explicitly connected to opportunities, an algorithm is developed to infer
indirect connections between activities and opportunities, using Contact and Account activity timelines.
Since these are not trivial connections (for example, an account may have multiple opportunities), AI is
assigning them appropriate predictive weights.
How the predictive opportunity scoring model is trained
First, we make sure, automatically, that the data we have is meaningful and contributing to the prediction.
Then we look at each recent activity level of every opportunity and try to find a correlation between this
signal and the likelihood of winning the opportunity.
After the model is trained, we can view the open opportunities in the system and give them a score based
on past examples.
What the AI does is learn how recent activity level affects the likelihood to win an opportunity in your
organization.








 Digital Downloads
Digital Downloads