Here’s what you need to know about Microsoft security Updates
To help organizations protect all their assets against evolving digital security threats, Microsoft is unifying all Extended Detection and Response (XDR) technologies under the Microsoft Defender brand.
Microsoft Defender prevents, detects, and responds to threats across identities, endpoints, applications, email, IoT, infrastructure, and cloud platforms.
With Microsoft Defender, Microsoft is rebranding the existing threat protection portfolio and adding new capabilities, including additional multi-cloud (Google Cloud and AWS) and multi-platform (Windows, Mac, Linux, Android, and iOS) support.
Microsoft Defender is delivered in two tailored experiences:
- Microsoft 365 Defender for end-user environments
- Azure Defender for cloud and hybrid infrastructure

Microsoft 365 Defender
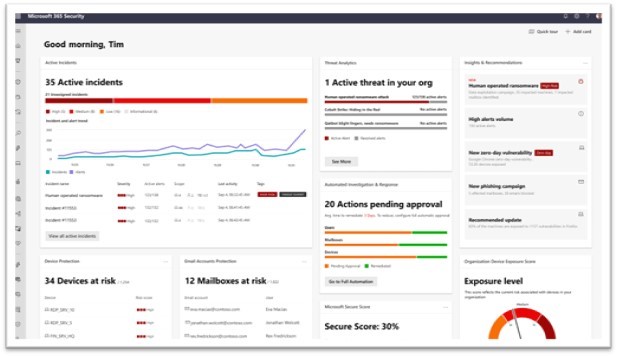
- Microsoft 365 Defender delivers XDR capabilities for identities, endpoints, cloud apps, email, and documents.
- It uses artificial intelligence to reduce the SOC’s work items.
- Built-in self-healing technology fully automates remediation more than 70% of the time, ensuring defenders can focus on other tasks that better leverage their knowledge and expertise.
The branding changes to unify the Microsoft 365 Defender technologies:
- Microsoft 365 Defender (previously Microsoft Threat Protection)
- Microsoft Defender for Endpoint (previously Microsoft Defender Advanced Threat Protection)
- Microsoft Defender for Office 365 (previously Office 365 Advanced Threat Protection)
- Microsoft Defender for Identity (previously Azure Advanced Threat Protection)
New features available within Microsoft 365 Defender:
- Extending mobile threat defense capabilities in Microsoft Defender for Endpoint to iOS, Android and macOS.
- Priority account protection in Microsoft Defender for Office 365 will help security teams focus on protection from phishing attacks for users who have access to the most critical and privileged information.
Customers can customize prioritized account workflows to offer these users an added layer of protection.
Microsoft 365 Defender
Azure Defender
Azure Defender delivers XDR capabilities to protect multi-cloud and hybrid workloads, including virtual machines, databases, containers, IoT, and more.
Azure Defender is an evolution of the Azure Security Center threat protection capabilities and is accessed from within Azure Security Center.
Microsoft has announced brand changes for these capabilities under Azure Defender as well:
- Azure Defender for Servers (previously Azure Security Center Standard Edition)
- Azure Defender for IoT (previously Azure Security Center for IoT)
- Azure Defender for SQL (previously Advanced Threat Protection for SQL)
New features now available within Azure Defender:
- To help defenders identify and mitigate unprotected resources, Microsoft is delivering a new unified experience for Azure Defender that makes it easy to see which resources are protected and which need further protection.
- Added protection for SQL servers on-premises and in multi-cloud environments as well as virtual machines in other clouds, and improved protections for containers, including Kubernetes-level policy management and continuous scanning of container images in container registries.
- Support for operational technology networks with the integration of Cyber X into Azure Defender for IoT.








